How Behavioral Health Centers Handle HIPAA Breaches
Behavioral health centers face unique challenges when managing HIPAA breaches due to the sensitivity of mental health and substance use disorder (SUD) records.
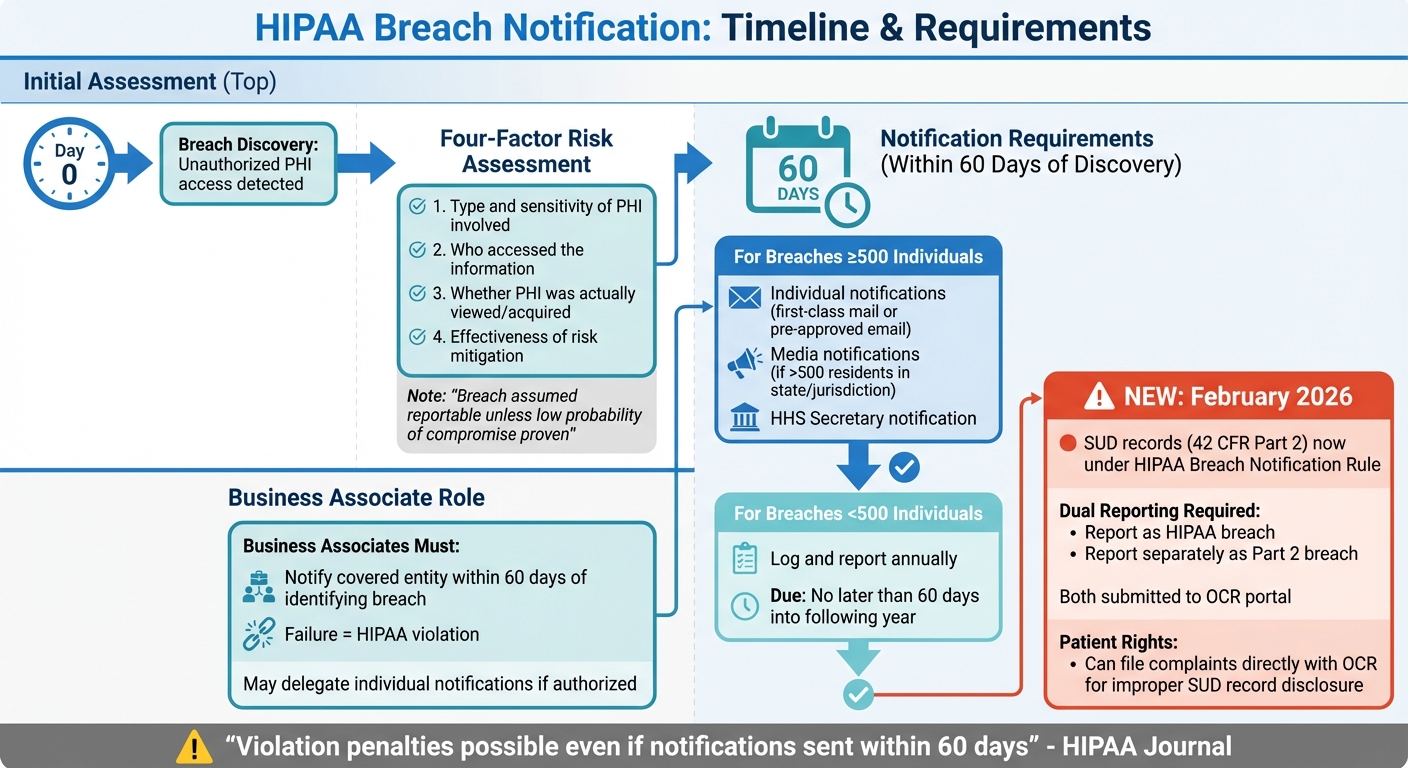
Breaches not only risk patient trust but also bring financial penalties and compliance scrutiny. With recent updates in 2026 aligning SUD record rules with HIPAA, centers must now navigate stricter reporting, risk assessments, and security measures.
Key points include:
HIPAA Breach Notifications: Centers must notify affected individuals, media (if over 500 people impacted), and the HHS Secretary within 60 days of breach discovery.
2026 Changes: SUD records now follow HIPAA breach rules, requiring dual reporting for combined PHI and SUD breaches.
Risk Assessments: Regular evaluations of vulnerabilities are mandatory, with fines for non-compliance reaching up to $2.19 million annually.
Security Safeguards: Administrative, physical, and technical measures like multi-factor authentication (MFA), encryption, and audit logs are critical to prevent breaches.
Recent cases, such as Deer Oaks’ $225,000 settlement, show the costly impact of weak security protocols. Modern EHR systems, like Opus Behavioral Health EHR, help centers stay compliant by offering advanced features like secure messaging, access controls, and automated risk management tools.
Behavioral health centers must prioritize robust security practices and updated protocols to avoid breaches and protect patient data.
HIPAA Breach Notification Rules and Deadlines
HIPAA Breach Notification Timeline and Requirements for Behavioral Health Centers
When Protected Health Information (PHI) is used or disclosed without authorization, behavioral health centers must act quickly.
According to the HHS Breach Notification Rule, any unauthorized access is assumed to be a reportable breach unless the organization can demonstrate a low probability that the PHI was compromised [5].
To prove this, centers must conduct and document a four-factor risk assessment. This assessment looks at: the type and sensitivity of the PHI involved (including identifiers and the chance of re-identification), who accessed the information, whether the PHI was actually viewed or acquired, and how effectively the risk has been mitigated [4][7].
Required Notification Steps
Once a breach is confirmed, specific notification rules and deadlines kick in.
Individual notifications: These must be sent via first-class mail (or email, if the patient has agreed to this beforehand).
Media notifications: For breaches impacting more than 500 residents in a state or jurisdiction, media outlets must be informed.
HHS Secretary notification: Breaches involving 500 or more individuals require notification to the HHS Secretary.All of these must be completed within 60 days of discovering the breach [4][1].
For smaller breaches, organizations can log them and report to the HHS annually, no later than 60 days into the following year [4].
Business associates also have a role to play. They must notify the covered entity within 60 days of identifying a breach. Failing to do so is considered a violation [7].
While the covered entity is ultimately responsible for notifications, they may delegate the task of notifying affected individuals to the business associate [4].
"It is possible to receive a HIPAA violation penalty for delaying notifications, even if they are sent within 60 days of the discovery of the breach." - Steve Alder, Editor-in-Chief, HIPAA Journal [7]
These tight deadlines highlight the importance of having updated protocols in place, especially with the changes coming in 2026.
2026 Updates to Breach Notification Rules
In February 2026, new updates will add another layer of complexity for behavioral health centers. Substance use disorder (SUD) records governed by 42 CFR Part 2 will now fall under the HIPAA Breach Notification Rule and the OCR reporting portal [6].
This means that if a breach involves both traditional PHI and Part 2 records, centers must report them separately - once as a HIPAA breach and again as a Part 2 breach [6].
Additionally, patients can now file complaints directly with the OCR if they believe their SUD records were disclosed improperly [6].
To comply with these updates, centers should revise their business associate agreements to ensure all security incidents are reported, even if they don't meet the formal definition of a breach.
Staff training will also be critical to help employees differentiate between PHI and Part 2 records, ensuring proper dual reporting [6][7].
Risk Assessment and Management Practices
Preventing security breaches starts with pinpointing vulnerabilities. The HIPAA Security Rule mandates that behavioral health centers conduct a formal risk analysis as the cornerstone of their compliance efforts, as outlined in 45 CFR §164.308(a)(1)(ii)(A) [10].
Interestingly, skipping this crucial step is the most frequent violation cited in Office for Civil Rights (OCR) enforcement actions [1].
For example, in February 2024, Green Ridge Behavioral Health settled with OCR for $40,000 after failing to conduct a proper risk analysis, which jeopardized the protected health information (PHI) of over 14,000 patients [1].
Similarly, Doctors' Management Services faced a $100,000 fine in 2023 for relying on a basic security questionnaire instead of a thorough analysis. These cases highlight that relying on quick fixes like a vendor-provided checklist does not meet OCR's standards.
"Conducting a risk analysis is the first step in identifying and implementing safeguards that comply with and carry out the standards and implementation specifications in the Security Rule."
HHS.gov [10]
While risk analysis identifies potential threats, risk management focuses on implementing measures to mitigate those risks.
Administrative, Physical, and Technical Safeguards
HIPAA outlines its security requirements in three main categories:
Administrative Safeguards: These involve policies, procedures, and people. Behavioral health centers must appoint a Security Officer to oversee HIPAA compliance and ensure regular workforce training, tailored to both clinical and non-clinical roles.
Following the "minimum necessary" rule, staff should only access the PHI they need for their job. Additionally, Business Associate Agreements (BAAs) are required for any vendor handling electronic PHI (ePHI) [3].
Physical Safeguards: These focus on securing facilities and devices. Examples include restricting physical access to areas with electronic systems or paper records, positioning monitors away from public view, using automatic screen locks, encrypting portable devices, and following proper disposal protocols for hardware [8].
Technical Safeguards: These rely on technology to protect ePHI. Key measures include strong access controls with unique user IDs and role-based permissions, mandatory Multi-Factor Authentication (MFA) for remote access starting in 2026, audit controls to monitor system activity, encryption for data in transit, and integrity controls to prevent unauthorized data alterations [1].
|
Safeguard Category |
Behavioral Health Example |
HIPAA Requirement Type |
|---|---|---|
|
Administrative |
Annual training on "duty-to-warn" vs. HIPAA privacy |
Required |
|
Administrative |
Executing BAAs with telehealth and billing vendors |
Required |
|
Physical |
Positioning EHR monitors away from patient view in group rooms |
Addressable |
|
Physical |
Locked server closets in residential treatment facilities |
Required |
|
Technical |
Mandatory MFA for clinicians accessing EHRs remotely |
Required (2026 Update) |
|
Technical |
Encryption for clinical notes sent via email |
Required (2026 Update) |
|
Technical |
Audit logs to track who accessed psychotherapy notes |
Required |
The Security Rule is designed to be adaptable, allowing organizations to implement safeguards that match their specific size and complexity. If a requirement is reasonable to implement, it must be adopted - or an equivalent alternative must be documented. These safeguards are essential for maintaining compliance.
How to Conduct Risk Assessments
Conducting a risk assessment involves seven key steps:
1. Define Scope: Identify all ePHI assets, such as EHRs, cloud storage, mobile devices, and telehealth platforms.
2. Identify Threats: Consider both natural risks (like floods or fires) and human risks (like hacking or insider threats).
3. Document Vulnerabilities: Record weaknesses, such as outdated software or weak passwords.
4. Assess Current Controls: Evaluate how effective your existing security measures are.
5. Determine Likelihood and Impact: Estimate the probability of threats occurring and their potential consequences.
6. Document Findings: Create a prioritized Risk Register.
7. Implement a Risk Management Plan: Address the gaps identified, focusing on the most critical issues first [11].
"The result [of a risk assessment] drives your entire HIPAA risk management program: what to fix, in what order, and to what standard."-
Bellator Cyber [11]
Behavioral health centers should pay particular attention to ensuring that EHR systems can separate sensitive records, like psychotherapy notes, from general records [3][9].
Additionally, substance use disorder records governed by 42 CFR Part 2 require strong consent management capabilities, and telehealth vendors must have BAAs in place.
With healthcare data breaches averaging $9.77 million in 2024 [11] and HIPAA civil penalties for willful neglect reaching up to $2,190,294 per violation category by 2025 [3], regular, well-documented risk assessments are critical.
These assessments not only ensure compliance but also lay the groundwork for a strong security program that protects patient data and minimizes financial risk.
Case Studies: How Behavioral Health Centers Responded to Breaches
Recent cases investigated by the Office for Civil Rights (OCR) highlight the steep costs of security breaches and the extensive corrective measures organizations must take to restore compliance.
Two incidents, in particular, underscore the financial and operational impact of inadequate security protocols.
Lessons from Recent OCR Cases
In July 2025, Deer Oaks – The Behavioral Health Solution agreed to a $225,000 settlement after two major security incidents. The first, a coding error in a discontinued pilot portal, exposed discharge summaries for 35 patients.
This data was indexed by search engines from December 2021 to May 2023.
The second, a ransomware attack in August 2023, compromised the electronic protected health information (ePHI) of 171,871 individuals. OCR's investigation revealed that Deer Oaks had not conducted a thorough risk analysis to identify vulnerabilities in its systems [12].
"OCR's investigation found that Deer Oaks failed to conduct an accurate and thorough risk analysis to determine the potential risks and vulnerabilities to the ePHI that it held."
HHS Office for Civil Rights [12]
Similarly, Green Ridge Behavioral Health LLC, a Maryland-based clinic, faced a $40,000 fine in February 2024 following a ransomware attack in 2019 that affected over 14,000 patients.
The OCR investigation, launched in December 2019, found that the clinic lacked essential security measures, had not performed adequate risk analyses, and failed to monitor its systems effectively. These shortcomings delayed the detection of unauthorized access [2].
Both cases reveal a pattern: a single reported incident often leads to broader investigations that uncover systemic security failures.
|
Behavioral Health Center |
Settlement Date |
Fine Amount |
Affected Individuals |
Primary Violation Cited |
|---|---|---|---|---|
|
Deer Oaks |
July 2025 |
$225,000 |
171,871 |
Failure to conduct an accurate/thorough risk analysis |
|
Green Ridge Behavioral Health LLC |
February 2024 |
$40,000 |
14,000+ |
Lack of security measures and adequate system monitoring |
These examples highlight the importance of addressing security issues promptly and comprehensively to prevent further risks.
Corrective Actions After Breaches
Both Deer Oaks and Green Ridge were required to undertake extensive corrective actions as part of their settlement agreements. These actions, paired with financial penalties, aim to ensure compliance and prevent future breaches.
Deer Oaks entered a two-year corrective action plan that included annual risk analysis updates, the development of a formal enterprise-wide risk management plan, and mandatory HIPAA training for all employees with access to patient data.
The organization must also submit implementation reports to the Department of Health and Human Services (HHS) to confirm ongoing compliance [12].
Green Ridge's corrective action plan imposed even stricter deadlines. The clinic had to submit a complete risk analysis to HHS within 60 days, create a Risk Management Plan within 90 days, and review all business associate agreements within 60 days.
Additionally, every workforce member was required to certify their understanding of HIPAA procedures [2].
These corrective measures reflect OCR's focus on proactive security measures rather than reactive fixes.
By treating risk analysis as a continuous process, organizations can better respond to emerging threats, whether from evolving ransomware tactics or vulnerabilities in new technologies like patient portals.
For example, Deer Oaks' prolonged exposure of sensitive data through a discontinued portal highlights the dangers of launching systems without thorough security testing [12].
These cases also demonstrate how HIPAA requirements and OCR expectations continue to evolve, pushing organizations toward a more vigilant and systematic approach to data protection.
How EHR Systems Help Prevent HIPAA Breaches
Modern EHR systems bring clinical documentation, communication, and data management into one secure platform. This setup not only minimizes areas vulnerable to attacks but also reduces the need for unsecured devices and external portals.
Features like integrated lab ordering and e-prescribing modules cut down on credential theft and data leaks by limiting the number of external system logins required [14].
Additionally, secure "no-app" patient engagement links enable encrypted communication through web browsers without storing sensitive health information on personal devices, which often lack proper security measures [16].
AI-powered tools for documentation play a key role by automating quality checks. This reduces human error and cuts documentation time by 40% [14].
Judd Carey, Director of Operations at VirtualServices, Mindful Health, highlighted the impact:
"By automating the quality of internal data, and applying an algorithm, it will cut back on errors to not miss a thing, especially from group sessions" [14].
This streamlined approach creates the foundation for specialized solutions like Opus Behavioral Health EHR, which takes HIPAA compliance to the next level.
How Opus Behavioral Health EHR Supports HIPAA Compliance
Opus Behavioral Health EHR employs advanced security measures such as multi-factor authentication (MFA), single sign-on (SSO), and strong encryption - 2048-bit TLS for data in transit and 256-bit for session tokens - to block unauthorized access [13].
The platform allows administrators to set precise access restrictions based on location, IP address, and time. These controls could have prevented many past unauthorized access incidents [13]. Opus also maintains detailed audit trails, logging every message and data access event. These logs fulfill the requirements for compliance audits by tracking the disclosure of information [15].
For addiction treatment centers, which must comply with 42 CFR Part 2, Opus addresses "Shadow IT" risks by replacing personal texting with secure, integrated messaging.
This feature operates as a Qualified Service Organization, ensuring all staff communications are encrypted and traceable [16].
Opus supports over 160,000 practitioners and has processed data for 44 million clients while adhering to certifications like PCI DSS Level 1, ISO 27001, and SOC 1 [13][14]. The platform also provides more than 140 detailed reports, helping administrators spot and address potential security risks early [14].
Beyond access controls, Opus includes tools for managing risks proactively.
Integrated Risk Management Tools
Risk management tools built into EHR systems provide around-the-clock security monitoring, including intrusion detection, firewall protection, and threat intelligence [13].
Automated alerts notify IT teams of unusual access patterns or vulnerabilities, enabling quick action to prevent data breaches.
This proactive approach is a stark contrast to the delayed responses seen in cases like Deer Oaks, where a coding error went unnoticed for 17 months, or Green Ridge, which took months to detect ransomware [12][2].
Consent tracking features further enhance security by ensuring patient authorization is verified before sharing data. This is especially important for facilities treating substance use disorders, where even revealing the facility name could identify someone as seeking addiction treatment - a violation of federal law [16].
Conclusion
HIPAA breaches in behavioral health come with serious consequences.
In 2025 alone, the Office for Civil Rights (OCR) closed 21 enforcement actions, marking it as the second-highest year on record. This highlights how critical it is for behavioral health centers to prioritize compliance as a core part of their operations, not just an afterthought [1].
Recent examples, like Green Ridge Behavioral Health's $40,000 fine and Beth Israel Lahey Health Behavioral Services' $70,000 penalty, demonstrate that no facility is exempt from enforcement [1].
Preventing breaches means conducting annual risk assessments and adhering to the 60-day notification rule.
With unified enforcement standards in place since February 16, 2026, Tier 4 violations now carry minimum fines of $73,011 and annual caps nearing $2,190,294 for substance use disorder centers [3]. These strict regulations make it clear that technology designed to enforce compliance is no longer optional.
Modern EHR systems built for behavioral health tackle common OCR concerns by offering features like role-based access and automated audit trails [1].
For example, Opus Behavioral Health EHR is designed with compliance in mind, integrating tools like multi-factor authentication and customized access controls.
As the 2026 regulations tighten, behavioral health centers that adopt such advanced EHR platforms can better protect themselves from costly fines and reputational harm [1]. Combining strong risk management practices with cutting-edge EHR technology ensures these centers stay compliant in an increasingly demanding regulatory environment.
FAQs
What counts as a HIPAA breach in behavioral health?
A HIPAA breach in behavioral health happens when protected health information (PHI) is accessed, used, or shared without proper authorization, jeopardizing its privacy or security. These breaches can occur either intentionally or accidentally. Regardless of intent, they violate HIPAA regulations and pose serious risks to patient confidentiality and regulatory compliance.
How do the 2026 Part 2 changes affect breach reporting?
The 2026 Part 2 changes have introduced updates to the HIPAA Breach Notification Rule, specifically addressing breaches involving substance use disorder records. Under these changes, entities are now required to report such breaches via a new OCR (Office for Civil Rights) portal.
This update aims to simplify the notification process and make breach information more accessible to the public. Aligning with these updated requirements helps ensure consistency with federal breach reporting standards.
What should be in a HIPAA risk analysis for a behavioral health center?
A HIPAA risk analysis for a behavioral health center involves carefully identifying and evaluating potential risks to the confidentiality, integrity, and availability of electronic Protected Health Information (ePHI).
This process examines technical, physical, and administrative safeguards to pinpoint weaknesses, address gaps, and prioritize steps to reduce risks effectively. To meet the requirements of the HIPAA Security Rule, the analysis must be detailed, consistently updated, and thoroughly documented - especially to ensure readiness for OCR audits or investigations.
